# QR Code Security Risks and How to Stay Safe
QR codes occupy a curious position in the security landscape. They are not inherently dangerous, but they are an excellent delivery mechanism for social engineering attacks because they hide the destination URL until after the scan. A user who would never click a suspicious link in an email will happily scan a sticker on a parking meter without a second thought, because QR codes have acquired an aura of legitimacy through their widespread use in payment, menus, and official contexts. Attackers have learned to exploit this trust, and the volume of QR-based phishing (now commonly called quishing) has grown sharply since 2022. This guide explains the actual threat landscape, the attack patterns that matter, and the specific habits and settings that keep users safe without making QR codes unusable.
---
## Why QR Codes Are a Security Concern
A QR code is essentially an obfuscated link. The user cannot read the destination before scanning, which breaks the normal trust signals that protect people from malicious URLs. On a computer, a cautious user hovers over a link to check the destination before clicking. On a phone looking at a QR code, there is no equivalent hover. The user commits to opening the URL at the moment of scanning, and only then sees what they opened.
Modern smartphones mitigate this by showing the decoded URL as a notification or preview before opening the page. This preview is the single most important defense against QR-based attacks, and many users ignore it. Training yourself to pause at the preview step and read the URL is the foundation of safe QR scanning.
| Threat Category | Attack Vector | Primary Risk |
|---|---|---|
| Quishing (QR phishing) | Malicious redirect to fake login page | Credential theft |
| Sticker overlay attacks | Physical sticker covering legitimate code | Payment or account hijack |
| WiFi honeypot codes | Fake WiFi credentials in QR | Traffic interception |
| Malicious app install | QR points at app store page for malicious app | Device compromise |
| Cryptocurrency address swap | QR contains attacker's wallet | Payment theft |
| vCard contact injection | QR installs malicious contact | Social engineering setup |
| Calendar bombing | QR adds spam calendar events | Ongoing phishing delivery |
| SMS premium fraud | QR triggers premium SMS | Direct charges |
---
## The Anatomy of a Quishing Attack
A typical quishing attack has three components: the lure, the landing page, and the credential capture.
The lure is the context that convinces a target to scan the code. Common lures include:
- An email claiming to be from the target's bank, asking them to "verify your account" by scanning a QR code
- A sticker on a parking meter that appears to offer a mobile payment option
- A flyer in a coffee shop promoting a WiFi signup
- An envelope labeled as "IRS tax refund" with a QR code to claim the refund
- A QR code in a corporate email that appears to lead to a mandatory training module
The landing page is a website designed to look like a legitimate service. Bank impersonation sites are the most common target because stolen banking credentials are immediately monetizable. Other common targets include Microsoft 365, Google Workspace, Amazon, and payroll systems.
The credential capture happens when the user enters their username and password on the fake page. Sophisticated attackers also capture two-factor authentication codes by passing them through to the legitimate service in real time, which defeats basic SMS and authenticator-app based 2FA.
> "Quishing works because it exploits the gap between our visual trust of QR codes and our ability to verify where they actually lead. A user who would never click a bit.ly link in an email will scan a QR code without thinking, because the scan feels like a physical interaction rather than a digital one."
>
> - Dr. Aaron Turner, SVP of Strategy at Hypori and former CSO, 2023 RSA Conference keynote
---
## The Sticker Overlay Attack
One of the most effective QR attacks against physical infrastructure is the sticker overlay. The attacker prints a QR code sticker with their malicious destination and physically applies it over a legitimate code on a parking meter, transit poster, restaurant table, or public information board. Users who scan the code are directed to the attacker's site rather than the intended destination.
This attack has been documented extensively against parking payment systems in Austin, San Antonio, and several European cities. Victims scan what appears to be the official parking payment code, are directed to a fake payment page, enter their credit card details, and lose both the parking payment and the card credentials to the attacker.
Defenses against sticker overlay attacks include:
- Agencies using tamper-evident codes (stickers that visibly tear if removed or covered)
- Physical inspection of codes before scanning (does the sticker look like it belongs, or was it applied over an existing surface)
- Prefer typing the URL from an official source rather than scanning the code
- Use the merchant's official app rather than the QR code pathway when possible
Restaurants have different sticker risk profiles because their codes are inside the venue and routinely inspected by staff. Hospitality venues like [Down Under Cafe](https://downundercafe.com) document weekly code-inspection procedures as part of their open/close checklist specifically to catch overlay attempts before they affect guests.
---
## WiFi QR Code Honeypots
QR codes encode WiFi credentials in a standardized format (`WIFI:T:WPA;S:network_name;P:password;;`). When a smartphone scans such a code, it offers to join the network automatically. This convenience is exploited by attackers who print WiFi QR codes in public spaces that lead to attacker-controlled networks.
Once connected to the attacker's network, the victim's traffic is visible to the attacker (for unencrypted connections) and vulnerable to manipulation through techniques like SSL stripping or DNS redirection. Captive portals on the attacker's network can capture credentials entered on fake login pages.
The defenses are specific to WiFi:
- Only scan WiFi QR codes at venues you trust and that have a clear reason to provide one
- Verify the network name with staff before joining
- Never enter credentials or make payments on an unfamiliar public network
- Use a reputable VPN when on public WiFi to protect traffic even on suspicious networks
- Disable automatic WiFi join for open networks on your device
---
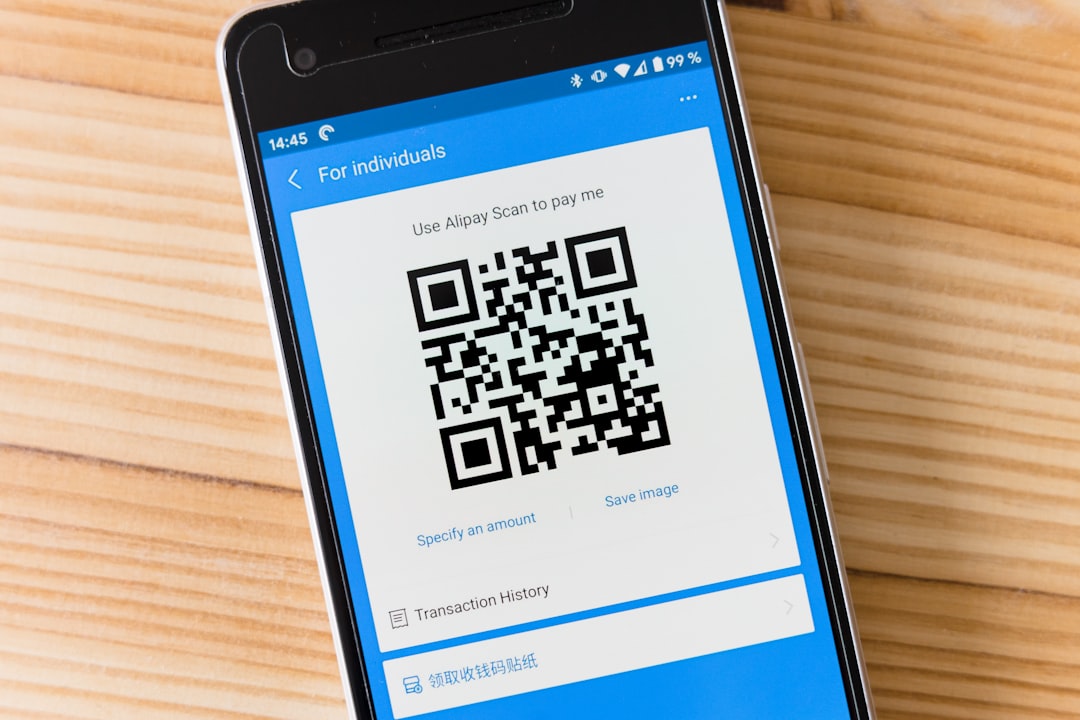
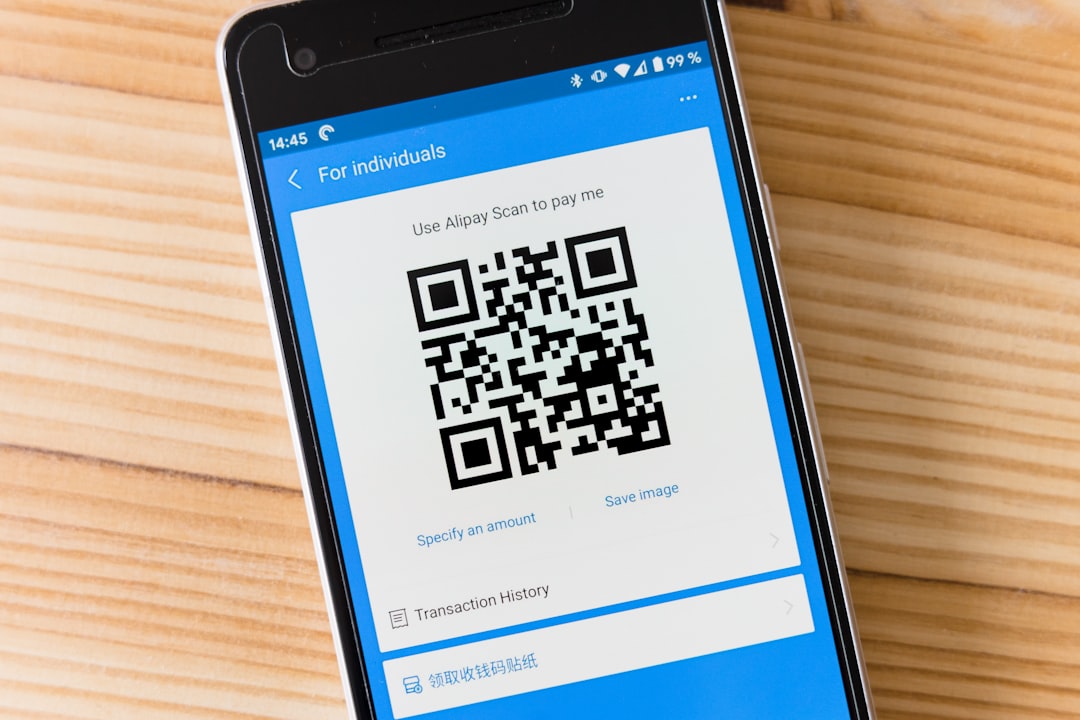
## Payment and Cryptocurrency Attacks
QR codes used for payments (both traditional and cryptocurrency) are high-value targets because the attack-to-payoff pathway is direct. Payment QR attacks typically work in one of three ways:
**Wallet address substitution.** In cryptocurrency payments, the QR code encodes a wallet address. An attacker who can replace the legitimate code with their own (through sticker overlay or by compromising the website showing the code) receives the payment directly. There is no way to reverse the transaction once funds are sent.
**Fake payment confirmation.** The user is directed to a page that looks like a payment processor but collects card details and other personal information without actually processing payment. The victim then has to pay again through the legitimate channel, having lost the card data in the meantime.
**Payment amount manipulation.** Some attacks use QR codes that pre-fill payment amounts higher than the user expects. On payment apps that auto-confirm QR-scanned payments, the user can lose significant funds before noticing the amount.
The practical defenses are to verify payment amounts before confirming, inspect wallet addresses for consistency with previous payments to the same vendor, and treat any unexpected or urgent payment request as suspicious regardless of how it arrived.
---
## Email-Based Quishing
Email quishing is the fastest-growing QR attack vector because it bypasses traditional email security. Email filters analyze URLs in messages, blocking known malicious domains. QR codes are images, not URLs, so the filter does not see the destination. The user scans the code with their phone, which is outside the filter's jurisdiction, and lands on the malicious page.
Microsoft reported in its 2023 Digital Defense Report that QR code phishing grew by 420 percent year over year, driven by corporate email attacks against Microsoft 365 credentials. Similar growth was reported by Proofpoint and Cisco Talos.
Corporate defenses include:
- Security awareness training that specifically addresses QR codes in email
- Email gateway products that decode QR code images and analyze the destination URLs
- Mandatory multi-factor authentication that resists replay (FIDO2, hardware keys)
- Reporting mechanisms so employees can flag suspicious QR-bearing emails
Individual defenses include:
- Treating QR codes in unexpected emails with the same skepticism as suspicious links
- Verifying any urgent request (password reset, payment, account verification) through an independent channel before acting
- Reporting suspicious QR codes to the apparent sender through a known-good contact method
---
## Scanner App Security
The QR scanner you use matters. Default camera-app scanners on iOS 15+ and Android 9+ are generally safe: they display the URL for preview before opening. Many third-party "QR scanner" apps in the app stores are malicious or abusive, collecting user data, inserting ads, or redirecting through their own servers.
Best practice is to use the built-in camera app for scanning whenever possible and avoid third-party scanner apps. If you need features the built-in scanner does not provide (continuous scan, history, batch scan), choose apps from reputable publishers with strong privacy policies.
Enterprise deployments often standardize on a single approved scanner app that enforces URL safety checking before opening. Security awareness training at organizations that follow the [professional development practices at Pass4Sure](https://pass4-sure.us) often covers QR scanner hygiene as part of general device security training.
> "The number of malicious apps pretending to be QR scanners in the app stores is genuinely surprising. For most users, the right scanner is the one already built into the phone. Any third-party scanner needs to earn its place by offering features the built-in cannot match, and it needs a clean privacy record."
>
> - Lookout Mobile Security Threat Report 2023
---
## Secure Generation Practices
If you generate QR codes for your business or personal use, you have a responsibility to generate them securely. This matters because users who scan your codes trust you to send them somewhere safe.
Key practices:
1. **Use HTTPS destinations.** QR codes pointing at HTTP URLs expose scanners to man-in-the-middle attacks on untrusted networks.
2. **Use your own domain in the URL.** Scanners should see a familiar domain when previewing the URL. Hiding behind a generic QR shortener reduces trust.
3. **Keep destinations stable.** If you use dynamic QR codes, avoid changing destinations abruptly in ways that could confuse returning users.
4. **Avoid redirector chains.** Each additional redirect is an opportunity for manipulation. Ideally the QR short URL redirects once, directly to the final destination.
5. **Monitor scan analytics for anomalies.** Unusual scan volume from a single geography or unusual times can indicate someone has copied your code and redeployed it elsewhere.
6. **Protect the generator account.** If you use a QR generator service, the account protecting it needs strong authentication. An attacker who takes over your QR account can redirect all your codes to malicious destinations.
When generating codes at a reputable tool like the [QR code generator at File Converter Free](https://file-converter-free.com/qr-code-generator), the generator does not control the redirect, which eliminates one class of risk. For dynamic codes you do want to use a provider with good account security and clean privacy practices.
---
## Mobile OS Protections
Both iOS and Android have built-in protections that reduce QR risk:
- **URL preview.** Both operating systems display the decoded URL before opening it, giving users a chance to inspect the destination.
- **Safe Browsing.** Both systems consult Google Safe Browsing (Android) or Apple's equivalent service to flag known malicious URLs before opening.
- **App store vetting.** Attempting to install apps from QR codes typically routes through the app store, where some vetting has occurred.
- **Sandboxing.** Browsers on both platforms sandbox web content, reducing the risk that a malicious page can escape the browser to attack the operating system.
These protections are not perfect but they are valuable. Keeping the operating system updated ensures you have the latest versions. Users running outdated OS versions miss recent safety-check improvements and are at higher risk.
---
## Organizational Policies
Businesses of any size should have documented QR code policies. At minimum:
- **Who can create official QR codes for the organization.** Controlled generation prevents rogue codes from proliferating.
- **Where official codes are deployed.** A public registry lets staff verify whether a code they see is legitimate.
- **How damaged or suspicious codes are reported.** A simple reporting channel catches overlay attacks and physical tampering.
- **How employees are trained on QR security.** Annual training on quishing and other QR-borne attacks reduces risk.
The business writing templates at [Evolang](https://evolang.info) include sample corporate security policies that cover QR code handling, which is increasingly an expected part of security awareness programs. Business formation guidance at [Corpy](https://corpy.xyz) now includes QR policy recommendations as part of standard startup IT setup, recognizing that even very small businesses need basic QR hygiene.
---
## What Users Should Actually Do
For most users, staying safe with QR codes comes down to a short list of habits:
1. **Preview the URL before opening.** Every time. Modern phones show the URL as a notification after scanning. Read it.
2. **Be suspicious of unexpected codes.** A QR code in an email you did not expect is a red flag, not a convenience.
3. **Inspect physical codes.** A sticker that looks applied over another sticker, or that sits on public infrastructure without obvious ownership, is suspicious.
4. **Never enter credentials on a page reached through a QR code.** If a login is genuinely required, navigate to the site independently and log in there.
5. **Use multi-factor authentication everywhere.** Preferably hardware-key or FIDO2 authentication that cannot be replayed by phishing sites.
6. **Keep your OS and browser updated.** Most QR-borne attacks exploit browser or OS vulnerabilities that are patched within weeks of discovery.
7. **Trust codes from verified sources more than from anonymous contexts.** A code in a laminated menu at a restaurant you have visited before is safer than a code on a flyer you found on the street.
These habits do not require refusing to scan QR codes. They require scanning them thoughtfully.
---
## The Cognitive Trap
Part of what makes QR-based attacks effective is cognitive. Research related to visual processing, including work explored in assessments at [Whats Your IQ](https://whats-your-iq.com), shows that users process QR codes using fast visual pathways and categorize them as "physical infrastructure" rather than as "digital links." This categorization causes users to apply physical-world trust signals (looks official, is in an official location) rather than digital-world trust signals (verified domain, HTTPS, known publisher). Attackers exploit this by placing malicious codes in contexts that look physically legitimate.
The defense is to re-categorize QR codes in your own thinking. Every QR code is a link, not a physical object. Treat it with the same skepticism you would apply to a URL in an unsolicited email.
Productivity tech coverage at [When Notes Fly](https://whennotesfly.com) has documented the behavioral shifts that reduce QR risk in practice, including the specific habit of pausing for one full second at the URL preview before opening any scanned link.
Even brief-format sites like [Strange Animals](https://strangeanimals.info) include QR codes in their printed educational materials, and they model best practices by using HTTPS destinations on stable domains. When you see a QR code in the wild, the quality of the destination is often a tell: legitimate publishers send you to branded domains, while attackers send you to generic redirectors or IP addresses.
---
## The Outlook
QR code attacks will continue to grow because the economics favor attackers. The cost of printing and placing a malicious sticker is near zero, while the potential payoff (stolen card data, compromised accounts, redirected payments) is substantial. Defenses will continue to improve: operating systems will warn more aggressively about suspicious destinations, email filters will decode QR images, and browser-level phishing protection will close more of the gap.
The long-term trajectory is toward a world where QR codes are safer by default but still require user judgment at the margins. Users who build the habit of inspecting URLs before opening them will be fine. Users who scan without thinking will continue to get caught by attacks that become more sophisticated over time.
The value of QR codes is too high to abandon them. Legitimate QR use cases (menus, payments, networking, authentication, boarding passes) deliver real convenience and productivity gains. The goal is not to stop scanning. The goal is to scan with the same caution you apply to any other link.
---
## References
1. Microsoft. "Microsoft Digital Defense Report 2023." https://www.microsoft.com/en-us/security/security-insider/intelligence-reports/
2. Proofpoint. "2023 State of the Phish Report." https://www.proofpoint.com/us/resources/threat-reports/state-of-phish
3. Focardi, Riccardo, and Flaminia L. Luccio. "Security Threats and Solutions for Two-Dimensional Barcodes: A Comparative Study." Network and System Security, 2019. DOI: 10.1007/978-3-030-36938-5
4. Yan, Zheng, et al. "A Comprehensive Study of QR Code Security: Challenges and Countermeasures." IEEE Access 9 (2021): 139345-139362. DOI: 10.1109/ACCESS.2021.3118726
5. Vidas, Timothy, Emmanuel Owusu, et al. "QRishing: The Susceptibility of Smartphone Users to QR Code Phishing Attacks." Financial Cryptography and Data Security, 2013. DOI: 10.1007/978-3-642-41320-9_4
6. FBI Internet Crime Complaint Center. "IC3 2022 Internet Crime Report." https://www.ic3.gov/
7. Krombholz, Katharina, Peter Frühwirt, et al. "QR Code Security: A Survey of Attacks and Challenges." Human Aspects of Information Security, Privacy, and Trust, 2014. DOI: 10.1007/978-3-319-07620-1_8
8. Lookout Mobile Security. "Mobile Phishing Threat Report 2023." https://www.lookout.com/threat-intelligence
guides
QR Code Security Risks and How to Stay Safe
Understand the real security risks of QR codes including quishing attacks, malicious redirects, WiFi hijacking, and payment fraud. Learn the scanner settings and behavioral habits that keep you safe.